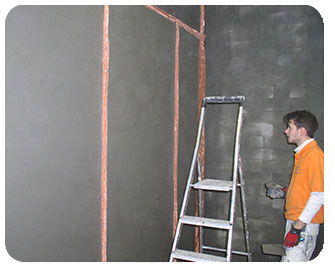
Shielded Rooms and Shielded Chambers with Cuprotect® |
||
|
|||||||||||||||||||||||||||||||
Shielding with Cuprotect® according to the Zone Model |
||
IT Shielding Strategies: The Zone Modelvan Eck Phreaking | TEMPEST | BSI Zone Model by the German Federal Office for Information Security (BSI) Function:All electronic devices, especially video display terminals (VDTs), emit electromagnetic radiation. These so-called compromising emanations can be captured with suitable equipment, even across large distances (over 100 m), in order to eavesdrop on data transmissions. Most notably, an attacker could reconstruct the video signal and display it on a second screen. The video signal is very well suited for being displayed quickly, but other components and signals can also be emitted, thereby unintentionally broadcasting processed information. In addition to the radiant emanation, there is also compromising conducted electromagnetic interference such as power fluctuations. The German Federal Office for Information Security (BSI) recommends in its IT-Protection Catalogues to use protected computers (zone 1 according to the Zone Model) for sensitive areas.
Security Safeguard Options
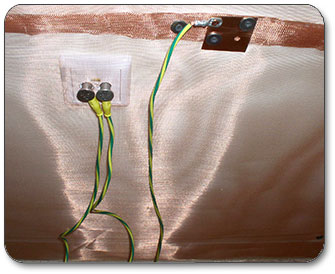
Cryptography is useless as a security safeguard because in this case it is not an encrypted data stream of a network that is tapped into but the electromagnetic radiation emanating from a video display terminal, which by definition displays the relevant information in an unencrypted form for the user to see. Cryptography is not used in this application. An effective, but at the same time highly expensive safeguard option is the complete shielding of a given workspace (based on the principle of Faraday’s cage), which would effectively shield against electromagnetic radiation. On the windows of such a workspace, transparent metal coating could be applied. As far as hardware is concerned, shielding strategies focus on shielding the components known to emit radiation such as graphic cards, cables, and monitors. For this reason, a central processing unit (CPU) is lined with a leakproof RF shield and cables are wrapped with foil shields and braided shields.
Low-emission or EMC/EMI-shielded devices may make van Eck phreaking more difficult. The emission level, however, should not be assessed based on such guidelines as the Swedish low-emission standard for VDTs (MPR II or TCO). The emission limits required for the TCO certification are set to avoid adverse health effects caused by EMF emissions from VDTs. This certification does not include any safeguards against compromising emanations. For the military-related sector, the German Federal Office for Information Security (BSI)—based on the NATO TEMPEST standards on compromising emanations—has developed a German version (called the Zone Model) that features three main zones (the standards were renamed at the end of 2006; the designation of the former NATO standards is given in parentheses): Zone 0 – NATO SDIP 27 Class A (AMSG 720B) Environment without special requirements Zone 1 – NATO SDIP 27 Class B (AMSG 788) Environment with medium level of protection (equivalent to 20 m free-space loss) Zone 2 – NATO SDIP 27 Class C (AMSG 784) Environment with high level of protection (equivalent to 100 m free-space loss)
With the exception of zone 0, the difference between zone 1 and 2 has to do mainly with the permissible limits for the specific power levels and specific bandwidths of the emanations. The exact limit values are classified information. Zone 0 equipment is also tested for information-carrying peak signals that are eliminated based on correlation.
In order to comply with these standards, one can request from the BSI the contact details for an accredited testing laboratory, which would run the required tests on the relevant hardware and, if desired, would also execute modifications accordingly. Testing according to the NATO standards is also available for the civil and commercial sector. At the present time, the BSI notes active testing in this market.
Low-pass filters can be equally effective for safeguarding analogue controls, even though to some extent they cause a considerable loss in quality as far as the recognition of details is concerned. Especially the display of text on a screen, which mostly consists of RF frequency components, can be made much more difficult to retrieve for eavesdroppers through the use of low-pass filters. The disadvantage for the user of the VDT, however, is that the low-pass filter causes especially the display of texts to appear blurry and thus is hard on the eyes. This strategy, therefore, is not suitable for permanent use at a workstation. Furthermore, it would only protect the video signal from transmitting compromising emanations. For analogue display terminals, the use of TEMPEST-proof fonts is a simple-toimplement safeguard. The characters of these special fonts are surrounded by contours with specifically adjusted colour gradients. The displayed result is similar to a two-dimensional low-pass filtering, and in some cases also lets the display of texts appear blurry. This safeguard, of course, is obsolete in digital displays because the digitised pixel data can again generate the signal. DVI-D displays operate with a different type of signal transmission (bit coding); it generates a bit pattern for each colour hue, including black and white. The latter fonts may even worsen the problem when the colour gradients of the displayed colours use a bit pattern that differs significantly from the bit pattern of the background colour across the spectrum under detection. The level of brightness and colour hue do not allow any identification of the bit code.
Power line filters and harmonic filters protect against compromising conducted electromagnetic interference. Another option is jammers. Jammers are designed in such a way that they transmit at a frequency (or frequency band) that coincides with that of the display terminal, but with a much higher amplitude. Because the Telecommunications Act specifies restrictions regarding maximum permissible power output levels, jammers may have to be operated at lower intensities and this, in turn, would provide eavesdroppers with a potential avenue that could allow them to filter or calculate out the desired signal. In this case, it is desirable to tie the jammer and the frequencies emitted by the display terminal together by using the RGB signals of the display terminal to modulate the jammer. Alternatively, the jammer could also be modulated with white noise so that a broadspectrum interference signal is generated. Source: Wikipedia
|
||
M 4.89 Electromagnetic Compatibility
To a certain degree, each electronic device emits electromagnetic radiation. These emissions are known as interference emissions and their maximum permissible emission level is generally regulated by law. In Germany, this is called the Electromagnetic Compatibility Act (EMVG). In devices that process information such as computers, printers, fax machines, modems, etc., the interference emissions can carry the processed information. This type of information-carrying emission is called compromising emanation. Should these compromising emanations be received some distance away such as in a house next door or a vehicle parked around the corner, the information contained therein can be reconstructed. Thus the confidentiality of the data is compromised. The emission limits of the EMVG are usually not sufficient to prevent the eavesdropping of compromising emanations. As a rule, additional methods are needed to provide protection against eavesdropping.
Compromising emanations can use different pathways to leave a space: In the form of wireless electromagnetic waves that propagate across free space like radio waves. As conducted electromagnetic interference along metal conductors (cable, ventilation ducts, heating pipes). Through coupling from a data cable into a cable running parallel to it. The emanation spreads across the parallel cable and can then be picked up at a far away distance. In the form of acoustic coupling into other devices. The transformation of sound into electric signals is facilitated by the sound-sensitive components of the devices that can act like a “microphone” under certain conditions. The subsequent transmission can run along metal conductors or also in the form of wireless electromagnetic radiation. Compromising emanations can also be caused by external manipulation of a given device. If a device is irradiated with RF radiation, for example, the internal electric processing of the device can be affected in such a way that the former RF radiation then carries the processed information. In all cases, the installation, i.e. the connections between devices and to the main grid, has a major impact on the propagation and thus also the reach of these emanations.
The German Federal Office for Information Security develops security strategies that effectively reduce the risk without a substantial increase in cost.
The Zone ModelThe Zone Model considers the propagation characteristics of compromising emanations under the various conditions of buildings and grounds. The attenuation of the emanations on their path from the emitting IT device to the potential receiver is measured. Depending on the conditions on site, it may be possible to use devices that require only minor or no special adjustments to eliminate electromagnetic interference. Elimination of Electromagnetic Interference at the SourceThis type of control strategy is especially suitable when new IT products are being developed. In this case, the compromising emanation is shielded at its source, inside the device where it is generated, or changed in such a way that it cannot be analysed anymore. This method, for example, allows the use of cost-effective plastic housing that has a negligibly small impact on the production price. Quick Testing ProcedureThe development of quick testing procedures and checks to see if a manipulation has occurred allows to ensure emanation security with a rather small effort—even after maintenance, repair, or possible unauthorized access. Use of Low-emission or EMC-shielded DevicesManufacturers of computer screens often promote their products with the term “low-emission” according to MPR-II, TCO, or SSI. These guidelines, however, only consider device emissions that may have adverse health effects. The testing procedures and limits for these emissions, therefore, are not suitable for the verification of compromising emanations and—like measurements for electromagnetic compatibility—do not allow for the evaluation of the level of protection provided against unauthorized data eavesdropping.
There are also specifically shielded IT systems. A detailed testing protocol by the BSI helps classify respective IT devices and systems according to their security level against eavesdropping. This concept is based on the idea of customizing security measures as much as possible to the user’s assumed level of threat, thereby minimizing the cost and optimizing the level of emanations security.
Originally, the BSI testing concept had been developed to protect classified government information, but it may also be useful in the business sector when data with high security requirements for confidentiality need to be protected. Thus, in many cases, a device compliant with the Zone Model and approved for use in zones 1 to 3 (a so-called “zone 1 device”) may already provide sufficient protection against the unauthorized eavesdropping of confidential information due to compromising emanations. The use of cost-effective zone 1 devices is therefore recommended by the BSI for those situations.
Whether a manufacturer offers shielded devices that meet the so-called TEMPEST criteria can be verified by contacting the manufacturer or the BSI, or by searching the official product listing BSI TL 03305, which is available online under the keyword “publications”. Keep in mind that the statement that a device is TEMPEST-certified still requires a reference to the specific security level it is approved for (e.g. approved for the use in zones 1- 3 according to the Zone Model).
Quelle: www.bsi.de
|
© 2010-2021 Cuprotect Shielding Systems GmbH | Am Bargfeld 15 | D-22941 Bargteheide | Tel:
+49(0)4532-6679
| Home | Shielding Effectiveness | Building Shielding | Shielded Chambers/Zone Model| Certified Training |
|
Special Applications | Shielding Design | Partners & Links | Contact | Imprint | Privacy Policy | E-Mail | cuprotect.eu |